![]()
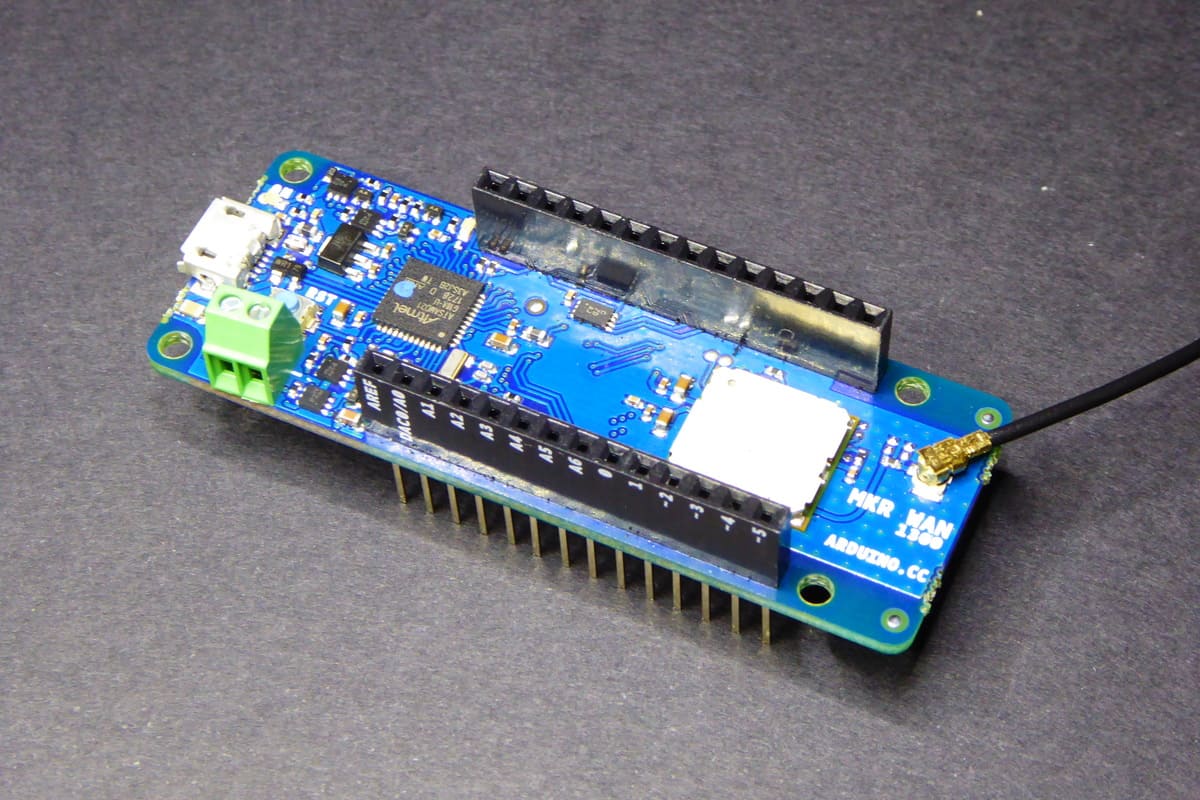
Arduino MKR WAN 1300
I've been testing quite a few LoRaWan nodes lately for TheThingsNetwork.cat, some based on HopeRF RFM95W (over AVR, ESP8266, ESP32,…) others using Microchip's RN2483 (an old friend of mine). I have a RAK811 waiting in the INBOX but the last one I've been playing with has been the new Arduino MKRWAN 1300 (so new there is no product page yet) and I liked it, quite a lot.
The device is one of the MKR series Arduino is pushing forward....
![]()
Using Google Assistant to control your ESP8266 devices
In my last post I tried to explain how to access your IoT devices at home from the Internet in a secure way using a reverse proxy. Truth is that I had it running since maybe 6 months ago without giving it too much use until recently. Reason? My Nexus 5 had been having serious problems (battery not charging, screen broken, earpiece not working,…) and I decided to replace it with a new mobile phone and the new one has Google Assistant built in....
![]()
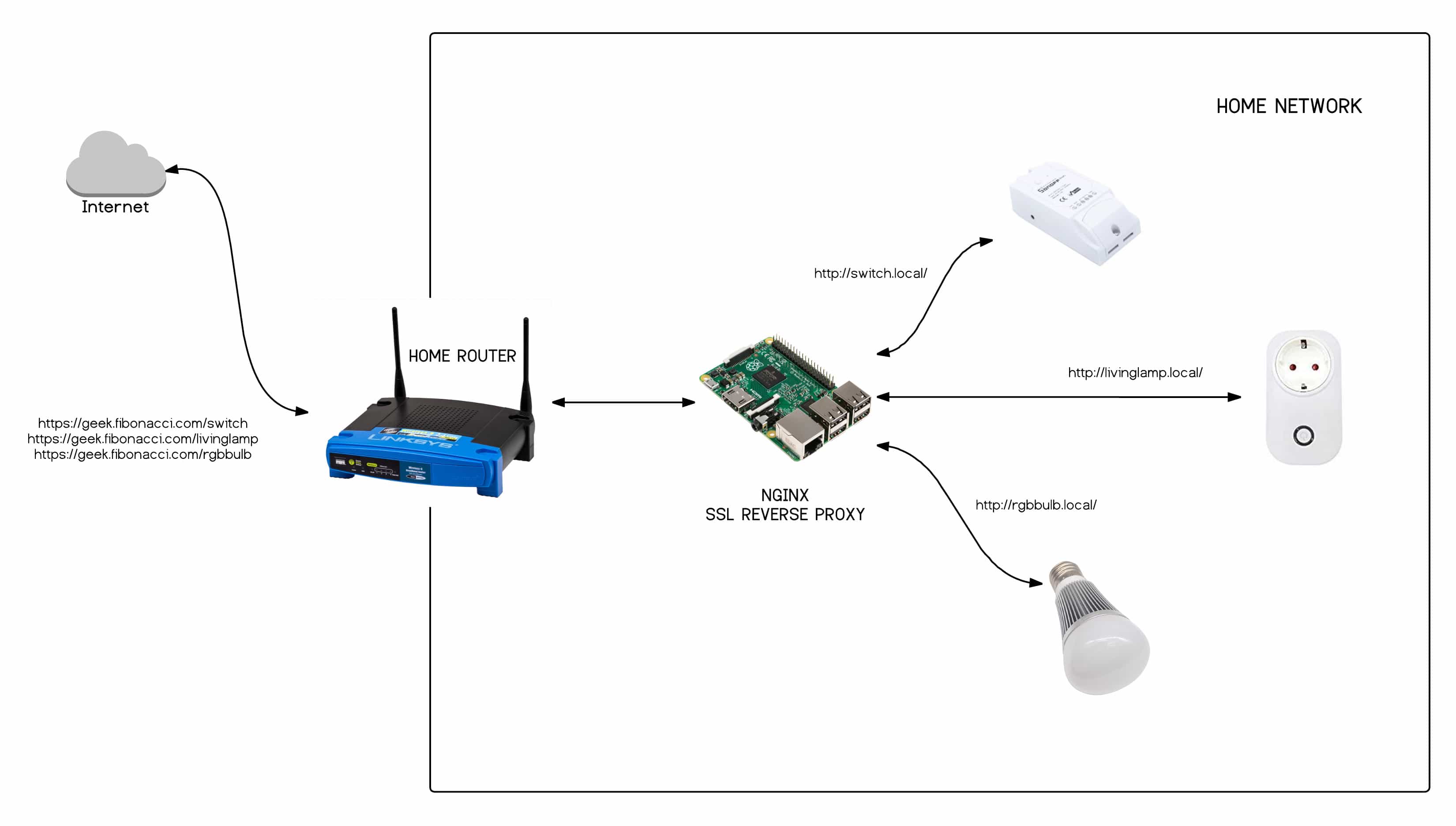
Secure remote access to your IoT devices
When you are hacking with IoT devices at home you get to face the challenge of accessing remotely to them, that is from outside your home network. I'm not saying your home network is a safe place, beware. But that thing outside, you know, “the Internet”, it's so scary… Unfortunately, most IoT devices are just not ready for the jungle. Neither the commercial ones, nor the hacked ones you might have....
![]()
Embed your website in your ESP8266 firmware image
A few months ago I wrote about the process I was using to optimize my website files for SPIFFS prior to upload them to the ESP8266. The goal was to reduce the number and size of the files to help the microcontroller to cope with them in an easier way. Smaller size mean faster downloads and less files mean less concurrency.
The process is done using Gulp, a tool to automate processes, and defined in a javascript file....
![]()
The mysterious IC
Sometimes Chinese manufacturers throw a mysterious, unlabelled, IC into their designs so we can spend a few hours trying to figure out what they are and what they do. It's such fun! I've been playing with one of those this afternoon, trying to answer those questions but also trying to understand why! Why is that chip there? Why did someone decided she needed that chip there?
Some weeks ago a user of ESPurna asked me if the firmware supported Itead's 1CH self-lock/inching board....
![]()
The HLW8012 IC in the new Sonoff POW
The HLW8012 is single phase energy monitor chip by the chinese manufacturer HLW Technology. It features** RMS current**, **RMS voltage** sampling and **RMS active power** with an internal clock and a PWM interface in a SOP-8 package. You can buy it at Aliexpress for less than a euro a piece and the necessary components are fairly easy to source and quite cheap.
All in all it looks like a great IC to include power monitoring in your projects....
![]()
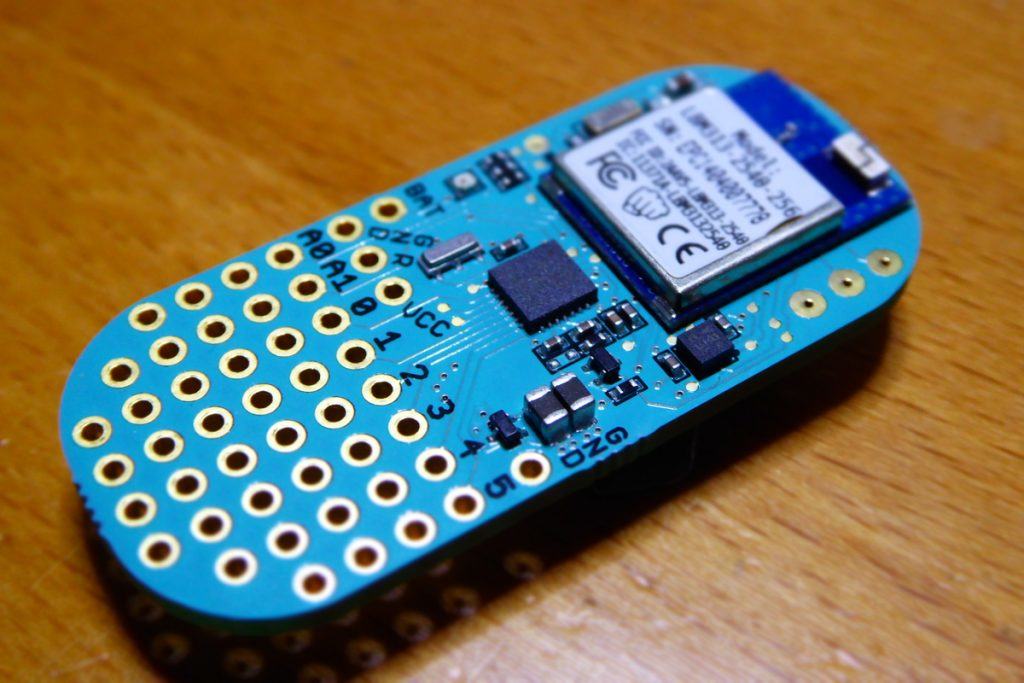
Using the new Bean Loader CLI from PlatformIO
Last Thursday PunchThrough, the people behind the LightBlue Bean and Bean+ boards, released their new Bean Loader, the application that allows you to upload new sketches to your beans. The great news about this is that, for the first time (!!!) the Bean Loader supports Linux!!! Yeeeha!
So I quickly looked for my 4 Beans that have been sad and forgotten in a components box for the last 2+ years and put them to work....
![]()
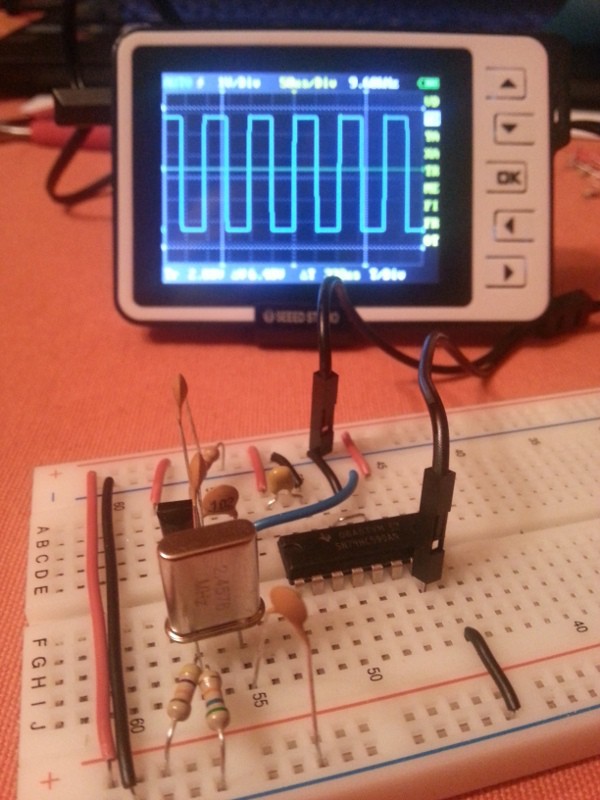
9600bps clock source
Quick post from an old draft, mainly as documentation.
A 9600Hz oscillator circuit based on a 2.4576MHz crystal and a 74HC590 binary counter. The idea was to reproduce the set up from robotroom.com site with a bar crystal but I had some trouble making it work. The solution came from this document about crystal oscillator circuits that describes different circuits depending on the crystal frequency. Here you have the schema and a picture of the circuit:...
![]()
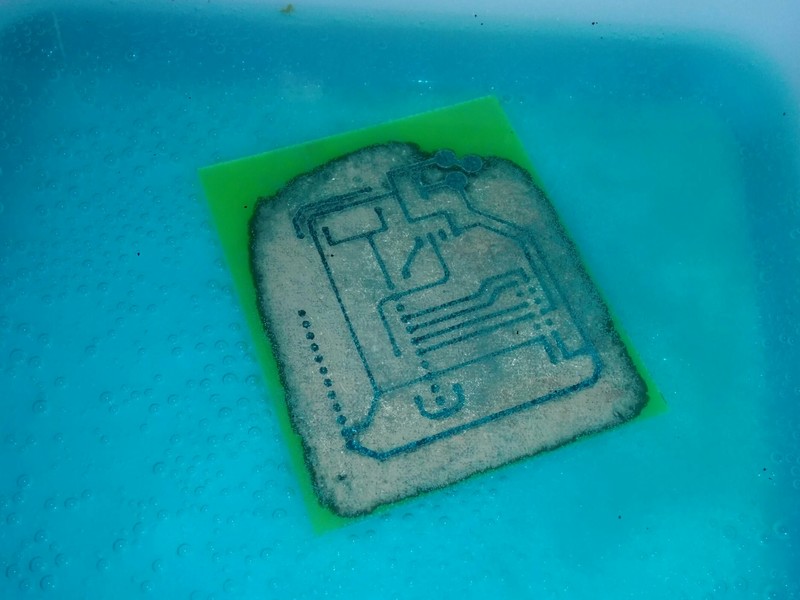
PCB etching at home using vinegar
PCB etching is another big topic in the electronics DIY world. It's something every electronics tinkerer ends up trying sooner o later. Even thou it's a fairly simple procedure it requires some self confidence (or bravery) since it involves strong, smelly and hazardous chemicals.
Any etching procedure you read about can be described in 5 different steps: designing, transferring, etching, assembly and reuse or disposal. For every one of these five steps there are different options and there are thousands of web pages with instructions, recommendations, how-to's… well, this is yet another one of those pages :)...
![]()
Ciseco XRF modules & LLAP Protocol
In my last post about counting events with Arduino and PCF8583 I talked about this “yet another weather station” project I was working on last summer. The station was deployed in the garden of a cute apartment we rented in an old “masia” near Olot, 100 km north of Barcelona. It is in the mountainside, surrounded by woods and 10 minutes walking from the near town. It has a beautiful garden with plenty of space....