![]()
Embed your website in your ESP8266 firmware image
A few months ago I wrote about the process I was using to optimize my website files for SPIFFS prior to upload them to the ESP8266. The goal was to reduce the number and size of the files to help the microcontroller to cope with them in an easier way. Smaller size mean faster downloads and less files mean less concurrency.
The process is done using Gulp, a tool to automate processes, and defined in a javascript file....
![]()
Itead Studio Sonoff SC Revisited
A few months ago I wrote about the Sonoff SC sensor hub by Itead Studio. It's a device with a Sharp GP2Y1010AU0F [Aliexpress] dust sensor, a DHT11 humidity and temperature sensor, an LDR as light sensor and a mic. The sensors are driven by an ATMega328P microcontroller but there is also an ESP8266 on board for WiFi communication, a pretty standard set up when you have several sensors and the ESP8266 GPIOs are just not enough....
![]()
A closer look at the H801 LED WiFi Controller
Some weeks ago I talked about the Magic Home LED Controller as I was adding support for it in my ESPurna firmware. At the time a user pointed me to the H801 Led WiFi Controller by Huacanxing. The user in question (Minh Phuong Ly) even did a pull request with some preliminary support for it. So I decided to give it a go.
The H801 is a 5 channels controller that you can find for about 9-10€ at Ebay or Aliexpress....
![]()
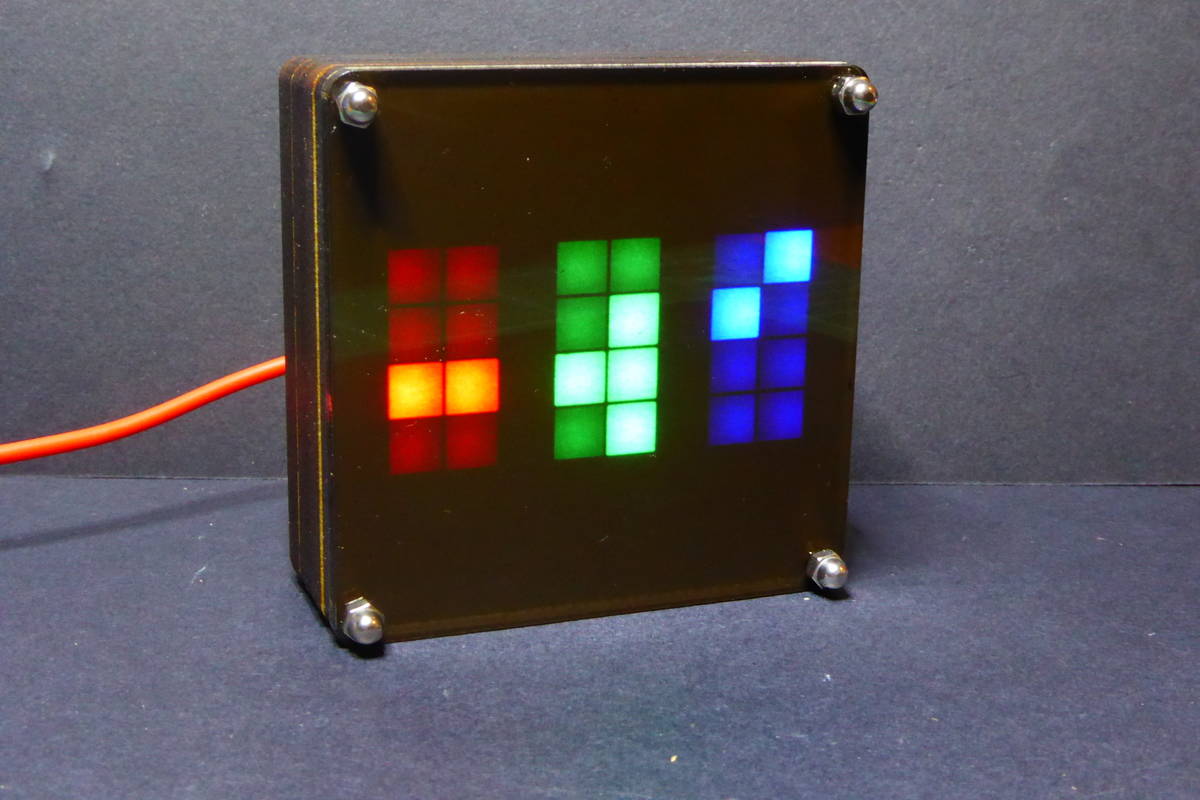
Slices of a clock
There are so many ways to tell the time. DIYers have been doing clocks since the Ancient Egypt (obelisks lacked portability, thou). Every modern maker has a clock amongst her first projects. I have done some myself, including a fibonacci clock, a wordclock with a fancy green matrix effect and an unreleased project that hopefully will see the light someday soon.
But recently I came back to the idea behind the wordclock before, to extend it in different ways:...
![]()
ESPurna smart socket
After a busy month I decided to spend some energy on doing hardware instead of software and the result was the ESPurna board I posted about just yesterday. The goal was to have a device based on the ESP8266 I could fit into my house wall gangs, with an SPDT relay to work with multi-way switches and power monitoring using the same IC the Sonoff POW uses: the HLW8012.
As a side project today I've been searching on the box of the TODO projects and I have rescued a KEMO STG15 [Ebay] plug housing with socket....
![]()
The ESPurna board, a smart wall switch with power monitoring
If you have read me, you might know I have a firmware for ESP8266-based smart switches called ESPurna. The firmware integrates with Alexa, Domoticz, Home Assistant and about any other service that supports MQTT or HTTP REST APIs. It supports a variety of devices, including almost the whole Sonoff family by Itead Studio, but also some other commercially available boards and light bulbs, and open source hardware projects as well....
![]()
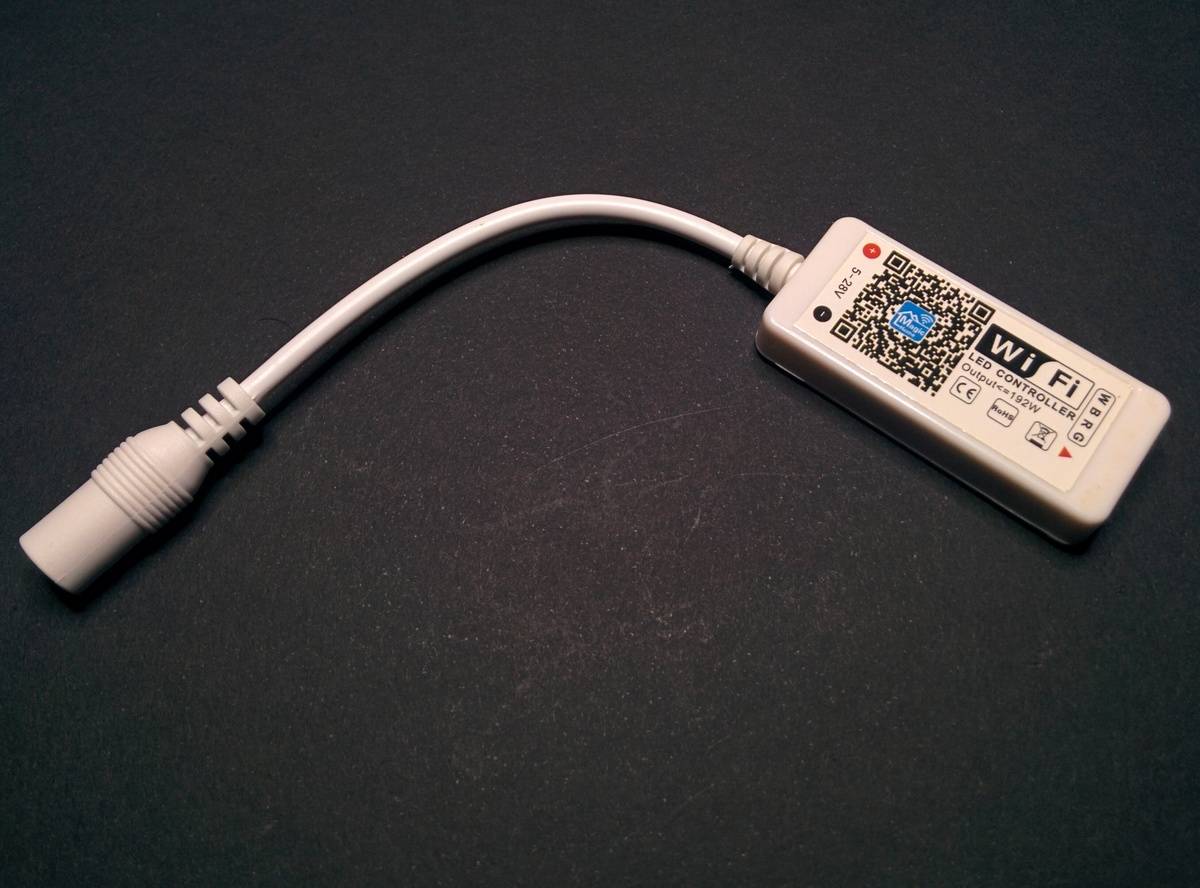
Magic Home LED Controller ESPurna'd
Following the bright path (sic) of the Ai-Thinker AiLight / Noduino OpenLight I wrote about a few weeks ago, now it's turn for one of those devices you purchase but once they arrive they are stored in the TODO box until they eventually come back to life.
The Magic Home LED Controller [Aliexpress, also available from Ebay] is an ESP8266 based single-color RGB(W) LED strip controller. It works with every 5050 LED strip [Aliexpress] out there....
![]()
KK2015 based Ai Light
Really busy these days. I have some drafts ongoing but I wanted to publish this short post right away.
One of the readers of this blog, Michel Clavette, sent me these pics just yesterday. He bought 5 Ai Light bulbs and to his surprise two of them do not have an ESP8266 microcontroller but instead this IC labelled KK2015.
KK2015 powered Ai Light. Picture by Michel Clavette It looks like a drop-in replacement for the ESP8266 since it has the same footprint and all the other components are (apparently) the same....
![]()
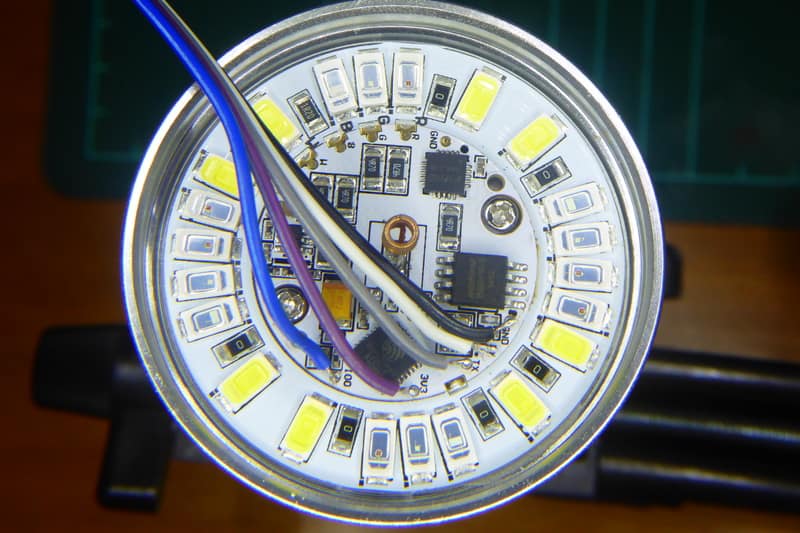
AiLight - A hackable RGBW light bulb
Some weeks ago a tweet by Manolis Nikiforakis (@niki511) with the #ESP8266 hashtag drew my attention. Manolis had just received a “smart lamp” branded by Ai-Thinker, the AiLight. Yes, the same Ai-Thinker that has sold millions of ESP8266 based modules. Chances were it had an ESP8266 microcontroller inside. Too good not to buy one and take a look at the inside.
Manolis shared the link where he bought his at Ebay for a bit more than USD 10 plus shipping....
![]()
The mysterious IC
Sometimes Chinese manufacturers throw a mysterious, unlabelled, IC into their designs so we can spend a few hours trying to figure out what they are and what they do. It's such fun! I've been playing with one of those this afternoon, trying to answer those questions but also trying to understand why! Why is that chip there? Why did someone decided she needed that chip there?
Some weeks ago a user of ESPurna asked me if the firmware supported Itead's 1CH self-lock/inching board....